Port forwarding
There are 3 possible types of port forwarding available for the SSH user. Serverauditor implements all of them. This section describes Dynamic forwarding, Local forwarding, and Remote forwarding and corresponding use cases. We'll start each subsection with a use case helping to understand what type of port forwarding should be used in a given situation
Dynamic and Local forwarding
Some admin at XYZ company is being asked to block any outstanding requests to the server at google.com. He goes to the rules of the company's firewall and blocks the domain. Since that time any attempt to open the website in a browser will be doomed. How to gain an access to the restricted domain from the office network?
To do so an employee needs to have a computer with SSH server installed which is outside the company's network (for example, employee-home-server.com). All he or she needs to do is to run the following command on the office machine from which the access to the restricted domain is required.
$ ssh -D 32000 [email protected]
This command will create a SOCKS server on top of SSH on the office computer. Now, if an employee points out localhost:32000 as a SOCKS proxy in his browser's settings, any traffic will pass through the employee-home-server.com domain and will not be blocked by the admin's firewall rules.
Let's now see how it works in Serverauditor. We are going to pretend that a user does not have an access to google.com from the office's WiFi. But suppose that 192.168.1.19 server is the only one which has such an access.
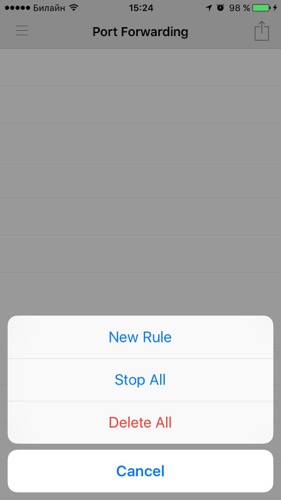
Go to main menu and open 'Port Forwarding'. Open a menu and select 'New Rule'.
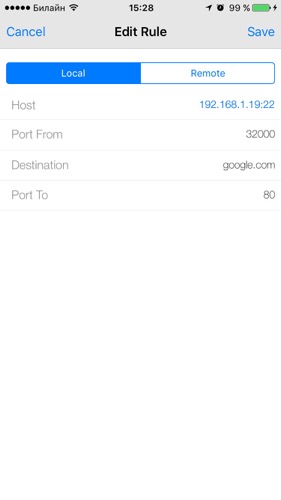
Fill in the fields as shown on the picture below. We are now interested in Local Forwarding option.
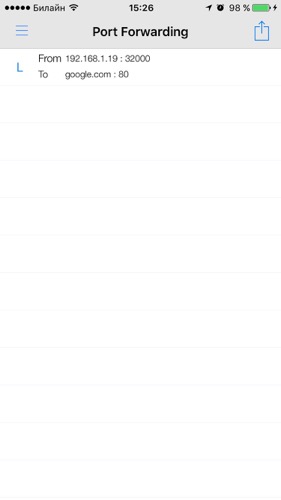
Open a browser and type localhost:32000 in the address field. You should be redirected to the google.com domain because localhost forwards all the requests on port 80 to the google.com domain now.